Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
June 2. Then again June 5.
A small hole in the network tore open. Not a metaphor — server logs don’t do metaphor. They timestamp. They point. They remember.
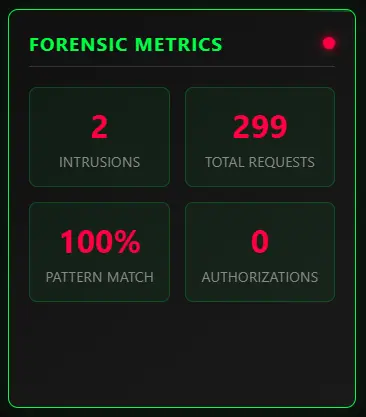
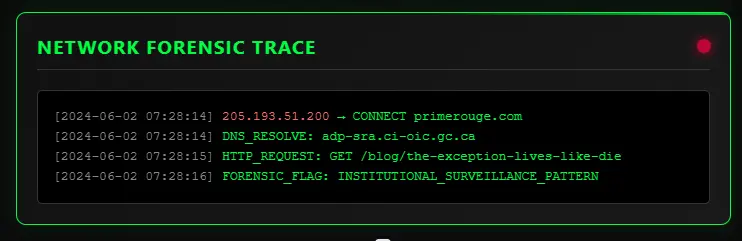
On two separate occasions, infrastructure belonging to the Office of the Information Commissioner of Canada (OIC) accessed behavioral metadata tagged to my firm, Prime Rogue Inc., while I was an active complainant in front of them. That infrastructure wasn’t anonymized. It wasn’t masked. It came in directly, leaving a signature: adp-sra.ci-oic.gc.ca.
In any other context, this would be misconduct. In the context of access-to-information oversight? It’s a constitutional breach.
What does it mean when the watchdog watches back?
This is not a metaphor either. It is a network event. It is two network events, in fact, crossing over a live complaint timeline like someone reaching across the chessboard to adjust both clocks. The OIC, while deliberating a section 6.1(1) application filed by Innovation, Science and Economic Development Canada (ISED), accessed digital properties associated with the very complainant named in that application.
They were not looking for context. They were not verifying delivery. They left a timestamp in the logs. The metadata — mine — said they arrived.
Canada’s access regime depends on one illusion above all: that the oversight body stands apart. That it adjudicates from a clean room, free of surveillance, conflict, and procedural scent.
But here’s the thing about the clean room: it never had a lock. And the metadata was watching it too.
This week, I filed a formal complaint against the OIC under section 30 of the Access to Information Act. The grounds are simple:
The firewall has failed. The institution is compromised. The oversight loop has closed.
The OIC wasn’t supposed to have hands — only eyes. It was never meant to manipulate the game board, only watch it. And yet, on June 2 and again on June 5, it reached in.
This is not a theory. This is not a poetic abstraction. This is 205.193.51.200, resolved to adp-sra.ci-oic.gc.ca, initiating requests against digital properties owned and operated by Prime Rogue Inc., during the precise window in which the Office was actively adjudicating a suppression request filed by Innovation, Science and Economic Development Canada.
To be clear: these were not systems check-ins. They were not mere crawls. The requests triggered surveillance flags — internal forensic markers that flag potential institutional probing based on header structure, behavioral timing, and session repetition. They walked like surveillance. They quacked like surveillance. They came from the regulator.
At the time of these incursions, the OIC had received a section 6.1(1) application targeting over 100 access requests I had filed — many of which directly pertained to misconduct, surveillance infrastructure, and interdepartmental metadata routing. I was not a passive litigant. I was an active subject.
And then they came looking.
We are meant to believe in procedural containment. That once a complaint is lodged, the complainant and the commissioner occupy different realms. That deliberation proceeds with neutral logic, bound by statute, free from impulse or retaliation.
But what happens when the architecture leaks?
What happens when the body assigned to adjudicate surveillance allegations commits an act of digital surveillance mid-process?
This isn’t a hypothetical. It’s logged. It’s timestamped. It has an IP.
It has a name.
Before the Office of the Information Commissioner ever acknowledged receipt of ISED’s section 6.1(1) application, I had already started unwinding the fuse.
Between May 31 and June 2, I issued nine separate communications — all timestamped, all in writing — narrowing, merging, or outright withdrawing over 70% of the access requests that ISED had claimed were “clogging” the system. These were not speculative gestures. They included explicit tracking numbers, scope reductions, temporal limits, and targeted clarifications. They were sent in good faith — and in plain text.
They were also ignored.
The OIC received that application. Then it watched my site.

The implications are not subtle. When an institution knowingly files a 6.1(1) application against a request set it knows to be defunct — and when the oversight body proceeds with that application despite notice of its mootness — we are no longer dealing with administrative oversight. We are dealing with procedural theatre.
The script has already been written. The clock is adjusted to match the act.
There is no published precedent for this. No directive that explains how to handle a 6.1(1) rendered moot before acknowledgment. There is only improvisation. And the improvisation, this time, involved digital surveillance.
So I filed again — under section 30(f). Not to quibble over volume, but to expose the structure.
Because if a requester cannot clarify or withdraw before the curtain rises — if the show must go on, even after the cast leaves — then the purpose of the Access to Information Act is no longer access. It is entrapment.
The watchdog is supposed to protect the citizen from the state. But what happens when the watchdog starts biting the complainant?
This isn’t allegory. This is behavioral posture — coded in responses, omissions, and strategically timed filings. In the days leading up to ISED’s section 6.1(1) submission, I narrowed over seventy access requests. Not in secret, not softly. I sent nine emails, named the tracking numbers, and restructured the scope. The response?
Silence.
Then, on June 2, the same day OIC infrastructure appeared in my logs, ISED finalized its Annex D upload — built around the now-defunct inventory. And the OIC didn’t blink. It processed the application anyway.
When I pointed out that the inventory had already changed — that the procedural basis for the suppression request had dissolved before acknowledgment — I was told that “these concerns can be raised within the 6.1(1) process.”
Within.
The same process now tainted by metadata surveillance, structural conflict, and institutional silence. A snake devouring its own tail — and calling it due process.
But the retaliation wasn’t just procedural. It was linguistic.
In ISED’s internal communications, clarification attempts were labeled “vexatious.” Metadata reformulation — flagged. Format accommodation requests — dismissed. Entire modes of digital self-defense were reframed as administrative aggression.
Meanwhile, the OIC — the body tasked with ensuring fairness — offered no firewall. No recusal. No procedural safeguard. Only access events in server logs, coming from infrastructure they never denied.
This is not neutral oversight. It’s reputational containment. It’s digital counterintelligence against a complainant under protection of statute.
And still, I’m expected to believe the decision will be fair.
Metadata has no ideology. It does not interpret, editorialize, or forget. It is the residue of infrastructure — time, origin, motion. And in systems that depend on plausible deniability, metadata becomes the only thing that cannot lie.
This is why they fear it.
When the Office of the Information Commissioner accessed my servers, they didn’t leave behind correspondence. They didn’t draft a note or call a meeting. But the logs preserved the truth: they were here.
In a bureaucracy built to deny, delay, or deflect, metadata functions as structural witness. Not a whistleblower, but a record that cannot be gagged. In this case, it shows that the oversight body was digitally monitoring the subject of an active complaint — during adjudication, during suppression attempts, during what is supposed to be the most procedurally sterile moment in Canada’s access system.
If the metadata proves this — and it does — then we are no longer debating administrative error. We are documenting institutional misconduct.
A society that cannot protect its metadata cannot protect its dissent. The logs do not care about justification. They only care about sequence. And the sequence here is fatal to neutrality:
The metadata shows where the clean room ends and where the wires begin. It exposes the real position of the observer.
It turns the oversight body into a participant.

They didn’t expect anyone to see it.
Not the access. Not the headers. Not the IP’s institutional signature. Not the coincidence of timing, or the systemic failure it implied. They especially didn’t expect the target to have telemetry — or to be watching back.
But I was.
I wasn’t filing access requests as a clerical exercise. I was mapping behavior. Testing reflexes. Probing the state’s periphery for signs of panic, overreach, or coordinated metadata choreography. What I found was not an abstract oversight failure. It was a live system, wired against the rights it was supposed to protect.
Surveillance is rarely confessed. It is inferred through timing, patterns, and reaction. But what the OIC gave me — inadvertently, clumsily — was something stronger: raw behavioral contact. A signal from inside the house. Twice.
And so, I filed.
But not just for myself. For the others who never saw the access, who don’t run forensic logs, who weren’t watching when the state looked back. For every citizen whose access request triggered invisible consequences — flagged, profiled, reclassified.
Filing became counter-surveillance. A public record not of what I sought, but of who watched me seek it.
The collapse isn’t theoretical anymore. It’s logged.
The OIC didn’t just breach neutrality. It burned the blueprint. And the smoke is visible in every decision they render without recusal, every delay cloaked in “administrative fairness,” every metadata trail they hope no one follows.
But the trail doesn’t vanish.
It lives in the long now of the access state.
The broader question is how many other people, ones who didn’t check server logs daily, did the OIC do this to?

You don’t need clearance to detect power. You need memory.
Not the memory of the institution — which forgets strategically — but the memory of the network. The memory of the logs. The cold fidelity of a system that records everything except remorse.
What happened here is not a one-off. It is a diagram — of how oversight corrodes, how institutions close ranks, how procedural language conceals structural violence. But it’s also a map.
And maps can be walked in reverse.
We are told that the access regime is collapsing under volume. But volume is not the threat — visibility is. The real panic starts when metadata exposes choreography, when filing becomes a mirror, and when the citizen refuses to blink.
So: file like it’s forensic. Write as if they’re reading — because they are. Treat access like counterintelligence. And always log the watchers.
The oversight loop is not broken. It is complete. Now we draw a new one — from the outside.
Because the watchdog doesn’t bark for us anymore.
But the infrastructure still speaks.
Wilco watches!
Wilco the Dog, Chief Security Officer of Prime Rogue Inc, 8 months and 70lbs, rescued from a frozen drainage canal in Vulcan County, AB, is here to make sure the OIC stops “hecking” around.

[…] From an analytical perspective, this represents something more dangerous than individual misconduct—it’s evidence of systemic institutional capture where Canada’s transparency watchdogs have become the predators. […]